教程详情
文件下载 | 文件名称:任鸟飞在线班74-81 | 文件大小:412.45MB |
| 下载声明:本站文件大多来自于网络,仅供学习和研究使用,不得用于商业用途,如有版权问题,请联系博猪! | ||
| 下载地址: 下载教程 | ||
教程目录:
任鸟飞2015在线班74天刀之BUFF遍历.exe
任鸟飞2015在线班75天刀之对象BUFF和技能预判.exe
任鸟飞2015在线班76天刀之摆摊和收摊.exe
任鸟飞2015在线班77天刀之摆摊标志位.exe
任鸟飞2015在线班78天刀之摆摊代工遍历.exe
任鸟飞2015在线班79天刀之摆摊移动CALL.exe
任鸟飞2015在线班80天刀狩猎100%命中.exe
任鸟飞2015在线班81天刀狩猎堆栈检测及关键点.exe
讲师 任鸟飞、骷髅
预告: 任鸟飞2016实地培训将于2016年3月份开课,年底前报名预交1000顶1500
详情请留意培训网址或咨询任鸟飞老师
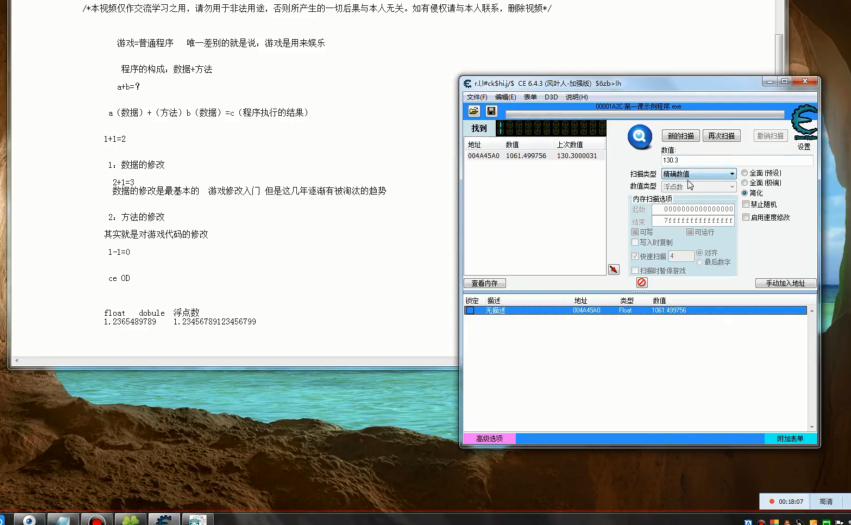
搜索1和0找到标志位,下写入断点
在二叉树下找到+10为6的节点,取+14为标志位,如果没有+10为6的节点说明此人没有摆过摊
00F8D911 8A45 08 mov al, byte ptr [ebp+8]
00F8D914 64:8925 0000000>mov dword ptr fs:[0], esp
00F8D91B 83EC 78 sub esp, 78
00F8D91E 53 push ebx
00F8D91F 56 push esi
00F8D920 8BF1 mov esi, ecx
00F8D922 57 push edi
00F8D923 3886 D4050000 cmp byte ptr [esi+5D4], al
00F8D929 0F84 68040000 je 00F8DD97 ; ESI坐标对象 取目标的对象
00F8D92F 8B8E AC070000 mov ecx, dword ptr [esi+7AC] ; [[esi+7AC]+C+4]二叉树 +14
00F8D935 8886 D4050000 mov byte ptr [esi+5D4], al
00F8D93B 84C0 test al, al
00F8D93D 74 5F je short 00F8D99E
00F8D93F 85C9 test ecx, ecx
00F8D941 74 09 je short 00F8D94C
00F8D943 6A 01 push 1
00F8D945 6A 06 push 6
00F8D947 E8 54FD4B00 call 0144D6A0
00F8D94C D9EE fldz
00F8D94E 8B0D 90C12702 mov ecx, dword ptr [227C190]
00F8D954 8B06 mov eax, dword ptr [esi]
00F8D956 8B90 18020000 mov edx, dword ptr [eax+218]
00F8D95C 83EC 14 sub esp, 14
===============================================================
0144D6A0 55 push ebp
0144D6A1 8BEC mov ebp, esp
0144D6A3 51 push ecx
0144D6A4 8B45 08 mov eax, dword ptr [ebp+8]
0144D6A7 53 push ebx
0144D6A8 56 push esi
0144D6A9 57 push edi
0144D6AA 8BF9 mov edi, ecx ; [ecx+4+C]+14
0144D6AC 8D4D FC lea ecx, dword ptr [ebp-4]
0144D6AF 51 push ecx
0144D6B0 8D4F 04 lea ecx, dword ptr [edi+4]
0144D6B3 8945 FC mov dword ptr [ebp-4], eax
0144D6B6 E8 7592FBFE call 00406930 ; 2222222222222222
0144D6BB 8338 00 cmp dword ptr [eax], 0
0144D6BE 8D55 FC lea edx, dword ptr [ebp-4]
0144D6C1 52 push edx
0144D6C2 8D4F 04 lea ecx, dword ptr [edi+4] ; [edi+4+C]+14
0144D6C5 0F9FC3 setg bl
0144D6C8 E8 6392FBFE call 00406930 ; 1111111111111111
0144D6CD 33C9 xor ecx, ecx
0144D6CF 384D 0C cmp byte ptr [ebp+C], cl
0144D6D2 8D55 FC lea edx, dword ptr [ebp-4]
0144D6D5 0F95C1 setne cl
0144D6D8 52 push edx
0144D6D9 8D4C09 FF lea ecx, dword ptr [ecx+ecx-1]
0144D6DD 0108 add dword ptr [eax], ecx ; 写入断点
0144D6DF 8D4F 04 lea ecx, dword ptr [edi+4]
0144D6E2 E8 4992FBFE call 00406930
0144D6E7 8338 00 cmp dword ptr [eax], 0
0144D6EA 0F9FC0 setg al
0144D6ED 3AD8 cmp bl, al
0144D6EF 74 54 je short 0144D745
0144D6F1 8B47 24 mov eax, dword ptr [edi+24]
0144D6F4 3B47 28 cmp eax, dword ptr [edi+28]
0144D6F7 73 11 jnb short 0144D70A
0144D6F9 8D48 04 lea ecx, dword ptr [eax+4]
0144D6FC 894F 24 mov dword ptr [edi+24], ecx
0144D6FF 85C0 test eax, eax
0144D701 74 14 je short 0144D717
===========================================================
00406930 55 push ebp
00406931 8BEC mov ebp, esp
00406933 8B41 0C mov eax, dword ptr [ecx+C] ; [ecx+C]+14
00406936 83EC 08 sub esp, 8
00406939 53 push ebx
0040693A 56 push esi
0040693B 8D71 04 lea esi, dword ptr [ecx+4]
0040693E 57 push edi
0040693F 8B7D 08 mov edi, dword ptr [ebp+8]
00406942 8BD6 mov edx, esi
00406944 85C0 test eax, eax
00406946 74 1A je short 00406962
00406948 8B1F mov ebx, dword ptr [edi]
0040694A 8D9B 00000000 lea ebx, dword ptr [ebx]
00406950 3958 10 cmp dword ptr [eax+10], ebx
00406953 7C 07 jl short 0040695C
00406955 8BD0 mov edx, eax ; eax+14
00406957 8B40 04 mov eax, dword ptr [eax+4] ; 右子树
0040695A EB 02 jmp short 0040695E
0040695C 8B00 mov eax, dword ptr [eax] ; 左子树
0040695E 85C0 test eax, eax
00406960 ^ 75 EE jnz short 00406950
00406962 3BD6 cmp edx, esi
00406964 74 07 je short 0040696D
00406966 8B07 mov eax, dword ptr [edi]
00406968 3B42 10 cmp eax, dword ptr [edx+10]
0040696B 7D 35 jge short 004069A2
0040696D 8B07 mov eax, dword ptr [edi]
0040696F 8945 F8 mov dword ptr [ebp-8], eax
00406972 C645 08 00 mov byte ptr [ebp+8], 0
00406976 8B45 08 mov eax, dword ptr [ebp+8]
00406979 50 push eax
0040697A 8D45 F8 lea eax, dword ptr [ebp-8]
0040697D 50 push eax
0040697E 51 push ecx
0040697F 8BC4 mov eax, esp
00406981 8910 mov dword ptr [eax], edx
00406983 8D55 08 lea edx, dword ptr [ebp+8]
00406986 52 push edx
00406987 C745 FC 000000>mov dword ptr [ebp-4], 0
0040698E E8 CD920301 call 0143FC60
00406993 8B45 08 mov eax, dword ptr [ebp+8]
00406996 83C0 14 add eax, 14
00406999 5F pop edi
0040699A 5E pop esi
0040699B 5B pop ebx
0040699C 8BE5 mov esp, ebp
0040699E 5D pop ebp
0040699F C2 0400 retn 4
004069A2 5F pop edi
004069A3 5E pop esi
004069A4 8D42 14 lea eax, dword ptr [edx+14] ; edx+14
004069A7 5B pop ebx
004069A8 8BE5 mov esp, ebp
004069AA 5D pop ebp
004069AB C2 0400 retn 4
教程截图
教程下载
原文链接:【教程宝盒网】 https://www.jc-box.com/3113.html,转载请注明出处。





请先 !